
Purchase Scams
In a purchase scam, individuals are tricked into paying for products or services that will never be delivered.
These scams often occur through counterfeit online storefronts, fictitious ads, or fraudulent listings that lure unsuspecting buyers. Scammers typically offer desirable, high-value items like vehicles, electronics, exotic holidays, or popular event tickets at unusually low prices to attract potential victims. While legitimate vendors usually provide secure payment options, scammers in these schemes coax buyers into choosing bank transfers for payment. The fraudster vanishes once the payment is made, leaving the victim with neither the product nor the money.
TALK TO A FRAUD FIGHTER
-
10%of consumers fall victim to deceptive online transactions each year.
-
5Bdollar annual global damages due to purchase scams.
-
45%of reported victims of purchase scams are individuals aged 30 to 50.
Thwart purchase scams.
ThreatMark can aid financial institutions in preventing purchase scams. By analyzing customers’ typical purchasing patterns and behaviors, ThreatMark can detect anomalies indicative of a scam, such as a sudden increase in transactions to new recipients or unusual payment methods, especially for high-value items. This is useful in spotting transactions diverging from a customer’s spending habits. When such irregularities are detected, the system can alert the financial institution, which can then take proactive measures.
Moreover, ThreatMark helps in understanding the evolving tactics of purchase scams. By monitoring transaction patterns across a broad spectrum of customers, these systems can identify new scam trends, such as specific types of products or services being used as bait in these scams. This proactive and adaptive approach empowers financial institutions to safeguard their customers’ funds effectively against the ever-changing landscape of purchase scams.

Techniques We Use to Stop Purchase Scams
-
Phishing Site Detection
Fraudsters use increasingly sophisticated methods to deceive users into revealing their login credentials. The fake pages they create are fully automated and very convincing, along with advanced evasion techniques to bypass traditional detection measures.
-
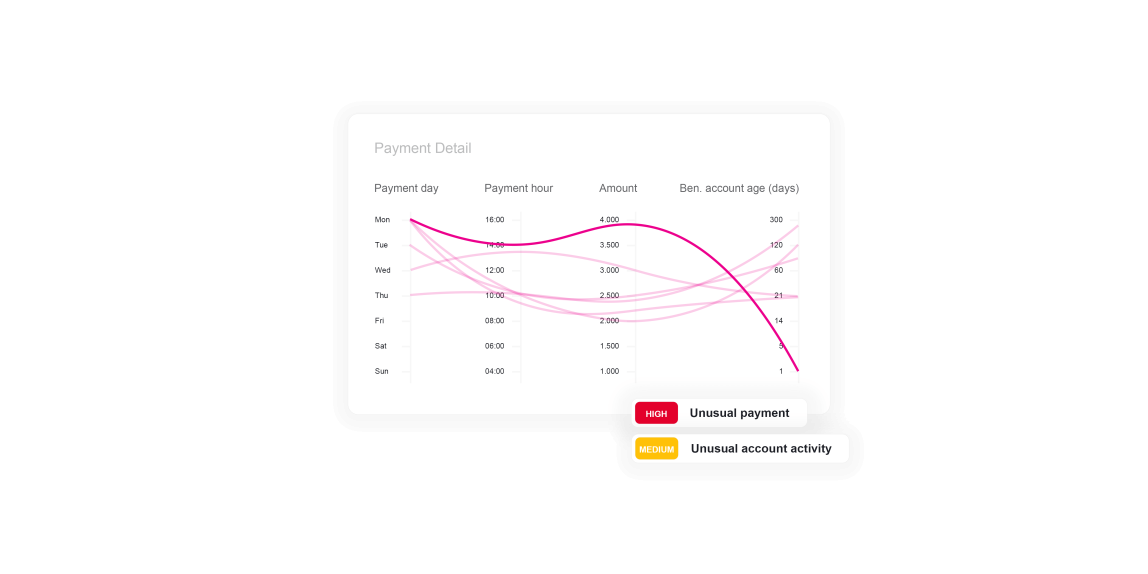
Abnormal Payment
The payment amount, time of day or day of the month of transfer, and the beneficiary can all be analyzed for risk to uncover if the payment is abnormal. Looking at the context of the payment in combination with other risk indicators can prevent fraudulent payments.
Want to learn more about ThreatMark?
Complete our form to discover more about ThreatMark’s comprehensive approach to fraud disruption.