New Account Fraud
New account fraud typically occurs when imposters use stolen or fake identities to open accounts.
New account fraud is particularly insidious because it can go undetected for long periods, giving fraudsters ample time to inflict significant financial damage and erode customer trust. ThreatMark helps counter account opening fraud using industry-unique behavioral insights into the client onboarding process, effectively sealing potential gaps.
Detect new account fraud with advanced behavioral biometrics & device intelligence.
TALK TO A FRAUD FIGHTER
ThreatMark’s approach starts prior to traditional KYC processes, bringing revolutionary behavioral insights to the new account onboarding process before identity verification happens.
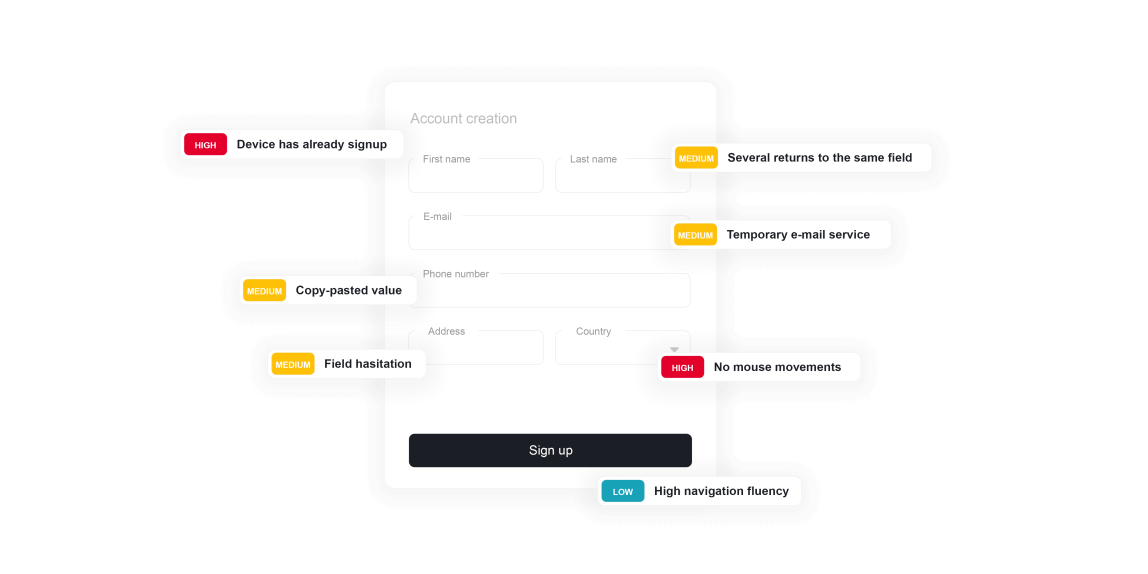
ThreatMark’s Behavioral Intelligence Platform captures user interaction details within the online application interface, scrutinizing cognitive and behavioral traits.
Using primary data collected by the Platform during user activity, such as mouse movements, typing cadence, navigation, and interaction with elements on a page, ThreatMark employs state-of-the-art machine learning methods to identify historically observed legitimate and criminal behavior patterns.
The scale of new account fraud.
-
2.43Bdollars was estimated that businesses would bear in fraud costs in 2023 due to synthetic identity fraud.
-
7%of all new accounts were fraudulent in the gaming sector.
-
1.8Bdollar increase in automotive lending, up from $1.3 billion in the same period the previous year, due to fraudulent applications.

Preventing new account fraud.
Types of New Account Fraud.
-
Bonus Abuse
ThreatMark can effectively identify and prevent bonus abuse in gaming and other banking environments by analyzing account creation and usage patterns and detecting anomalies that could indicate fraudulent activity. By recognizing these patterns, the Platform enables gaming organizations to take proactive measures, such as invalidating fraudulent accounts and their transactions, thereby protecting the integrity of its promotional campaigns.
Learn More
-
Bot Attacks
Studies show that at least 65% of individuals use the same password across multiple accounts, putting both the banks' and clients' money at risk if credentials are compromised. ThreatMark's Behavior Intelligence Platform employs cutting-edge technology to harness behavior analytics, effectively identifying the specific differences between bot and human behavior.
Learn More
-
Loan Fraud
ThreatMark can successfully identify discrepancies suggesting fraudulent activity by analyzing application patterns and applicant behaviors. With behavioral intelligence and machine learning methods, inconsistencies in application data, along with unusual speeds in filling out forms or atypical patterns in navigating the loan application process, are just some of the common traits flagged as fraudulent application activity. These key insights enable the institutions to scrutinize suspicious users more closely before allowing the transaction.
Learn More
FAQ: New Account Fraud
-
How does New Account Fraud occur?
Fraudsters acquire personal information like social security numbers, addresses, and names through data breaches or illicit purchases on the dark web. Using this information, they create bank accounts, credit lines, or loans under the victim’s name.
-
What are common signals of New Account Fraud?
ThreatMark can flag inconsistencies in application data, unusual speed in filling out forms, or atypical patterns in the new account application process, which are common in fraudulent applications.
-
About S.O.V.A. Malware Family
Our SOC team has reverse-engineered the peculiar S.O.V.A malware family. In this article read about the uniqueness of S.O.V.A. malware, how it works and some very peculiar details, namely: cookie stealing and its evolution in the cyber wilderness.
Read More
-
Security Issues Threat Actors Can Exploit In The Metaverse And How To Prevent Them
Digital identity theft is a major security concern in the online world today. With Metaverse being predicted to be the next phase of the internet and social interaction, such threats will continue with virtual profiles in the new realm, too. Solutions like ThreatMark are the perfect antidote to these security issues.
Read More
Want to learn more about ThreatMark?
Complete our form to discover more about ThreatMark’s comprehensive approach to fraud disruption.

